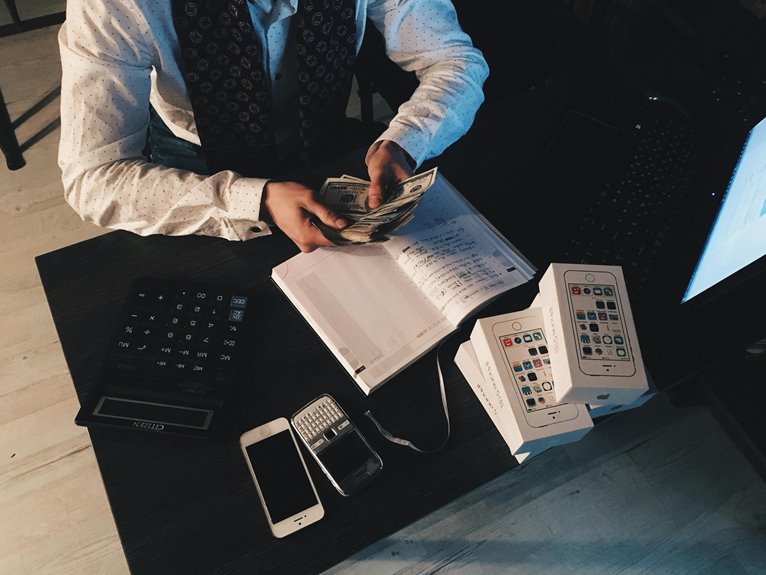
Caller data integrity is a critical concern in high-stakes environments, where a misstep can erode trust and obscure provenance. The sequence of identifiers and the substantial sum underscore the need for deterministic transformations, traceable logs, and end-to-end validation. A disciplined pipeline must expose gaps quickly and support auditable governance. The question remains: where do current controls fail, and how can they be strengthened to prevent hidden inconsistencies from compromising situational awareness?
Why Caller Data Integrity Matters in High-Stakes Environments
Caller data integrity is essential in high-stakes environments because even minor inaccuracies can cascade into critical errors, misinformed decisions, and unsafe outcomes.
The analysis notes how missed data and timing gaps degrade situational awareness, erode trust, and complicate accountability.
A skeptical lens reveals systemic vulnerability, urging precise capture, validation, and continuous scrutiny to preserve operational freedom and reliability.
Build a Robust Validation Pipeline for Every Touchpoint
A robust validation pipeline for every touchpoint is essential to ensure data integrity across stages, from capture to storage and retrieval. The analysis scrutinizes process boundaries, monitoring input provenance, and enforcing constraints without overreach. Callers data must be vetted at entry, transformed deterministically, and logged. A well-architected validation pipeline balances automation with auditability, supporting reliable, freedom-respecting data ecosystems.
Detecting Anomalies and Reconciliation: From Flags to Fixes
Detecting anomalies and reconciliation requires a disciplined approach that converts irregularities into actionable insights. The process emphasizes disciplined scrutiny of data lineage, tracing origins, transformations, and dependencies to isolate deviations. Anomaly naming standardizes signals, enabling consistent classification and communication. Reconciliation translates flags into fixes, prioritizing impact, feasibility, and traceability, while maintaining skepticism about noise. Clear documentation supports auditors, operators, and freedom-loving analysts seeking transparent accountability.
Governance, Compliance, and Continuous Improvement for Caller Data
The analysis emphasizes data governance maturity, auditable policies, and accountability.
Skeptical scrutiny reveals gaps in data lineage tracing, validation beyond ingestion, and continuous monitoring, ensuring freedom to adapt while preserving trust and traceability.
Conclusion
Conclusion (75 words, third-person, juxtaposition, analytical and skeptical):
In the ledger of crisis, integrity glints like a coin—bright at entry, blurred by entropy at retrieval. The pipeline promises traceability, yet shadows of drift persist between validation gates and audit logs. Proactive governance gleams as a lighthouse; complacency hums as a fog. Systems hum with precision, while humans weigh uncertainty. Ultimately, certainty is an ongoing wager: relentless checks against quiet deviations, or data, once trusted, becomes half-remembered noise.