Account & Call Log Validation for the listed identifiers requires careful alignment of format, ownership, and cross-system consistency. The approach must respect consent, minimize data use, and ensure transparent governance. A scalable, auditable workflow is essential to balance fraud prevention with user trust. Stakeholders should anticipate potential gaps between systems and prepare clear documentation. The discussion will address verification methods and risk controls to justify ongoing improvements. The next considerations will reveal practical implementation choices.
What Is Account & Call Log Validation and Why It Matters
Account and call log validation is the process of confirming that account information and call records are accurate, complete, and consistent across systems. This practice supports reliability, traceability, and accountability. Effective procedures employ standardized checks and audit trails. Risks arise from incomplete data or mismatches. Key goals include timely detection, transparency, and informed decision making. Keywords: Account validation, Call verification.
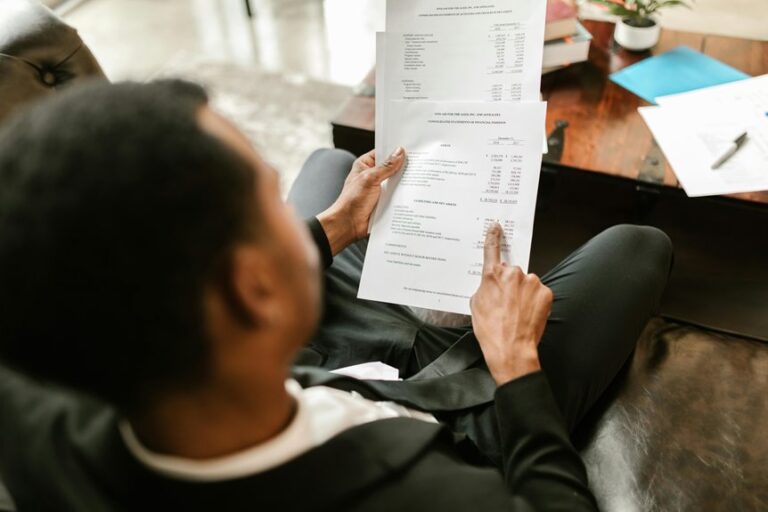
How to Verify Usernames and Phone Numbers Responsibly
To verify usernames and phone numbers responsibly, organizations should implement layered checks that confirm format, ownership, and consistency across systems. This process supports accountable Account verification and clear Phone consent.
Verification should rely on minimal data collection, auditable trails, and user-friendly prompts. Regular reviews reduce drift, while consented, transparent practices reinforce trust and align with freedom-minded governance.
Balancing Fraud Prevention With Privacy and Consent
Organizations should implement layered controls that detect suspicious activity without overreaching user privacy, ensuring transparency about data use and clear avenues for consent management.
This balance supports fraud prevention, privacy consent, safe handling, and data minimization while preserving user freedom and trust.
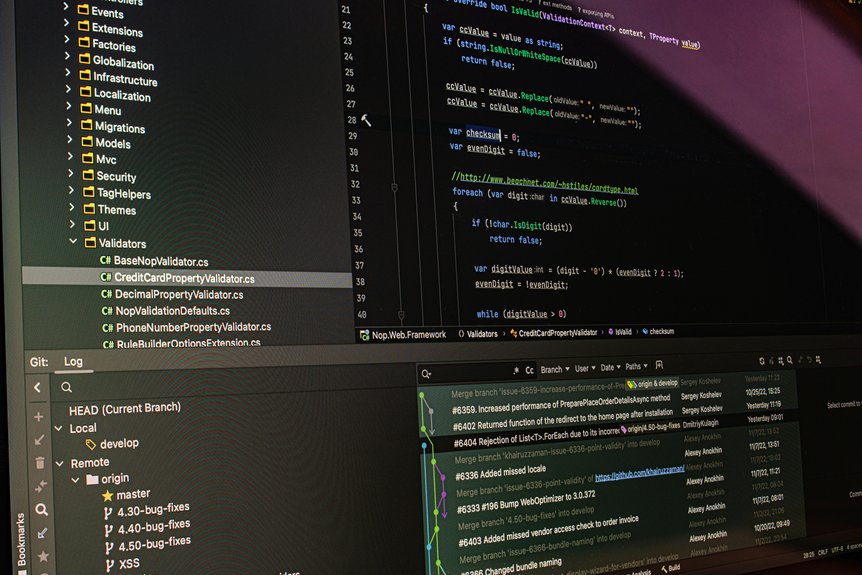
Implementing a Compliant, Scalable Validation Workflow
A compliant, scalable validation workflow builds on privacy-conscious fraud controls by codifying verification processes that are auditable, repeatable, and adaptable to changing risk patterns.
The approach emphasizes account validation and phone verification as core checks, integrates automated risk scoring, and maintains clear governance.
It enables rapid scaling, while preserving user trust and regulatory alignment across evolving threat landscapes.
Conclusion
Service-wide account and call log validation must uphold accuracy, consent, and privacy while remaining auditable and scalable. Verified identifiers and cross-system checks support trust and compliance, yet data minimization and governance controls guard user rights. When effectively balanced, the workflow functions like a lighthouse: clearly signaling legitimate, traceable activity without exposing sensitive shores. In this way, fraud prevention and privacy coexist, guiding operations with caution, transparency, and responsible stewardship.