The discussion centers on reviewing and verifying caller information accuracy for the listed numbers by initiating owner verification and source confirmation, then cross-checking against authoritative datasets to triangulate legitimacy. The process requires documenting each step with time-stamped evidence, preserving audit trails, and ensuring reproducible procedures. It will evaluate call histories for legitimacy, resolve conflicts with corroborated data, and escalate only when signals indicate misrepresentation or irrelevance, recording decisions prior to escalation. A cautious, methodical approach will guide practitioners toward clear criteria and consistent outcomes.
What to Verify About a Caller: Ownership, History, and Legitimacy
A prudent caller verification process begins by confirming three core elements: ownership of the account or telephone line, the caller’s historical context, and overall legitimacy. The approach emphasizes owner identity, corroborated ownership history, and a rigorous legitimacy verification.
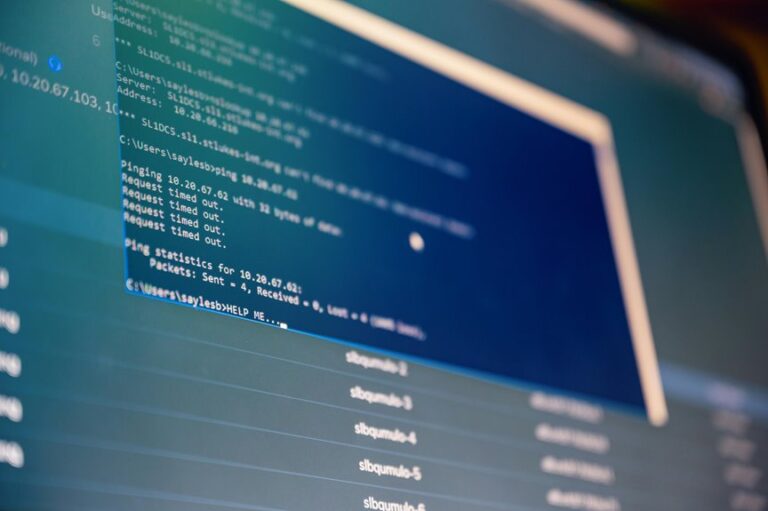
Tools That Make Verification Practical and Quick
The practical verification workflow relies on a suite of tools designed to accelerate accuracy without compromising rigor. Tools for authentication streamline cross-checks and conflict resolution, while data sources are triangulated to confirm legitimacy.
Detached evaluation emphasizes reproducibility, audit trails, and standardized queries. This approach preserves freedom by enabling rapid yet defensible decisions, reducing manual drudgery without sacrificing accountability or traceability for callers.
Step-by-Step Verification Process for Each Number
To verify each number, a structured, repeatable procedure is followed: collect the number, confirm its source, cross-check against authoritative data sets, and document each step with time-stamped evidence. The process emphasizes ownership verification, call history legitimacy assessment, and tool usage to ensure accuracy. Record results clearly, preserve provenance, and maintain transparent audit trails for future reference.
Troubleshooting and Red Flags: When to Ignore or Escalate
In the course of caller information verification, investigators must recognize when signals indicate misrepresentation or irrelevance and determine whether to ignore or escalate accordingly.
When verify ownership or verify history raises doubt, assess legitimacy through corroborated data, and escalate to appropriate channels.
If signals are inconsistent or unsupported, verify history, assess legitimacy, and document decisions before moving to escalation or dismissal.
Conclusion
To verify caller information for the listed numbers, follow a rigorous, repeatable method: initiate owner verification and source confirmation, cross-check against authoritative datasets, triangulate data, and document each step with time-stamped evidence to preserve an audit trail. Evaluate call histories for legitimacy, resolve conflicts with corroborated data, escalate only when signals indicate misrepresentation or irrelevance, and record decisions prior to escalation. Maintain reproducible procedures, and preserve traceable, auditable outcomes for all ten numbers.