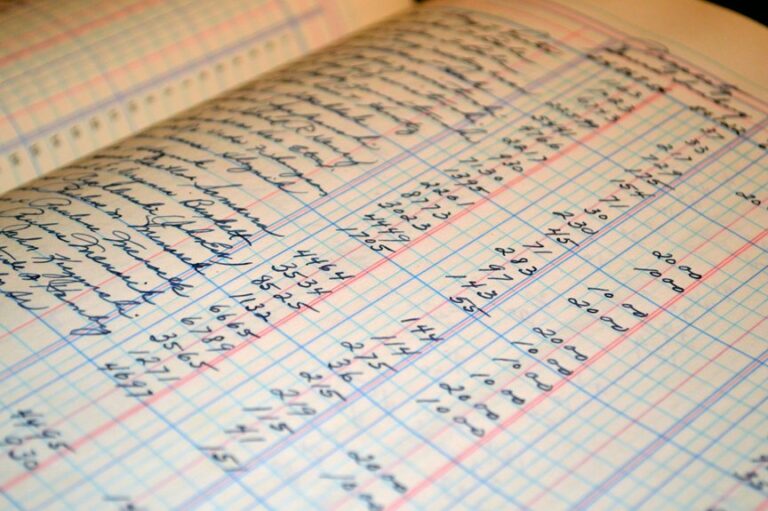
Validation of incoming communication records, including the listed numbers, requires a disciplined approach to source authentication, timestamp integrity, and recipient alignment. The discussion should address sensor calibration, metadata integrity, and provenance, applying cryptographic checks and anomaly detection. A rigorous audit trail is essential for ongoing governance and rapid containment of spoofing or fraud. Stakeholders will want clear criteria, repeatable processes, and measurable indicators before moving to implementation, with attention to potential edge cases and the need for transparent controls.
What It Means to Validate Incoming Communication Records
Validating incoming communication records involves verifying that each entry accurately represents the source message, its timestamp, and the intended recipient, while excluding any alterations or duplications.
The process emphasizes sensor calibration and metadata integrity, ensuring consistent data provenance. It dissects record lineage, confirms cryptographic integrity, and requires clear, auditable trails—supporting freedom through transparent, reproducible validation practices and disciplined documentation.
Practical Validation Checks You Can Run Now
Practical validation checks can be implemented immediately by systematically verifying core attributes of each incoming record: source credentials, timestamp integrity, and intended recipient alignment, while ruling out duplicates and tampering.
The process emphasizes Validation checks, anomaly detection, and compliance logging, enabling transparent fraud handling.
Methodical routines identify inconsistencies, document findings, and support freedom-oriented governance without compromising efficiency or security.
Handling Spoofing, Fraud, and Anomalies Effectively
Organizations must address spoofing, fraud, and anomalies with a structured response that builds on prior validation work. The approach emphasizes proof-based verification, layered controls, and rapid containment.
Spoofing prevention relies on strong identity attestation, cryptographic checks, and trusted metadata.
Anomaly detection uses baseline behavior, statistical thresholds, and cross-channel correlation to flag suspicious patterns for timely review and remediation.
Logging, Monitoring, and Compliance for Sustained Trust
How can a structured approach to logging, monitoring, and compliance sustain trust across an organization? A disciplined framework records events, reinforces accountability, and enables validation processes. Continuous monitoring detects anomalies, ensuring timely responses and evidence trails. Compliance practices codify expectations without stifling autonomy, promoting transparency. Clear metrics, auditable logs, and disciplined governance cultivate durable trust and enable informed decision making.
Conclusion
This validation framework provides a meticulous, end-to-end approach for incoming communication records, ensuring source authentication, timestamp integrity, and recipient alignment while eliminating duplicates and tampering. By enforcing sensor-calibrated metadata, cryptographic proofs, and auditable provenance trails, it supports transparent governance and rapid containment of spoofing or fraud. Through anomaly detection and rigorous logging, organizations gain a trustworthy baseline for evidence-based decisions, keeping risk at bay and operations running smoothly, rain or shine, to boot.